It’s probably a good idea to block t.co domains for a little while3 min read
The social media world is going through a shake-up right now. Just in case anyone wasn’t tracking, the world’s richest man, Elon Musk, just...
Creating a Remote Pi-Hole for Your Whole Home5 min read
The world has been in a weird state for the last few years. A global pandemic has disrupted human and material capital resulting in...
What happened to Gravitywall over the last month, and what did I learn?1 min read
You might have noticed over the last month that Gravitywall Blog was down; I know I got a couple of messages on Reddit about...
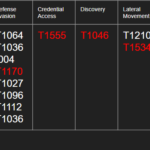
Incorporating MITRE ATT&CK in your Security Operations9 min read
Now I know what you’re probably thinking, oh great another blog post about MITRE ATT&CK, and I get it. MITRE has taken the cybersecurity...
Setting up Cloudflare Tunnel with Proxmox4 min read
I am a huge fan of Proxmox, I use it as my Type-1 hypervisor; however I travel frequently for my job and don’t always...
Pi-Hole messed up my Kindle Fire: but I fixed it3 min read
DNS based ad-blocking is great, until it’s not. I’ve wrote a lot about Pi-Hole, pfBlockerNG, Ad-Guard, and other services. I’ve used DNS based ad-blockers...

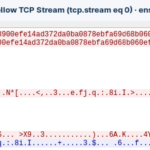
My Favorite Interview Question for Threat Hunters12 min read
Several years ago, I was responsible for interviewing applicants applying for a threat hunting position. I was one of a few managers who would...

AdGuard Home vs. Pi-Hole vs. PfBlockerng: What’s Better for your home network?17 min read
Ads suck. That’s why I don’t run any. Ads have dominated the internet over the last decade, it’s hard to go to any webpage...
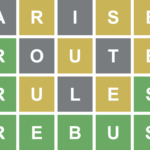
Improving my Wordle solver even more9 min read
And putting it online for the world The other day I wrote about how I improved my wordle solver using Bash scripting. This was...

Improving my Wordle Score with scripting5 min read
So, the other day I wrote about how to use grep to solve wordle and I’ve been using that method to crush the scores...
